Get unmatched application assessment services with next-generation integrated analysis technology
iAppSecure provides unmatched application assessment services with Fusion, an advanced next-generation technology that radically changes the way applications are assessed.
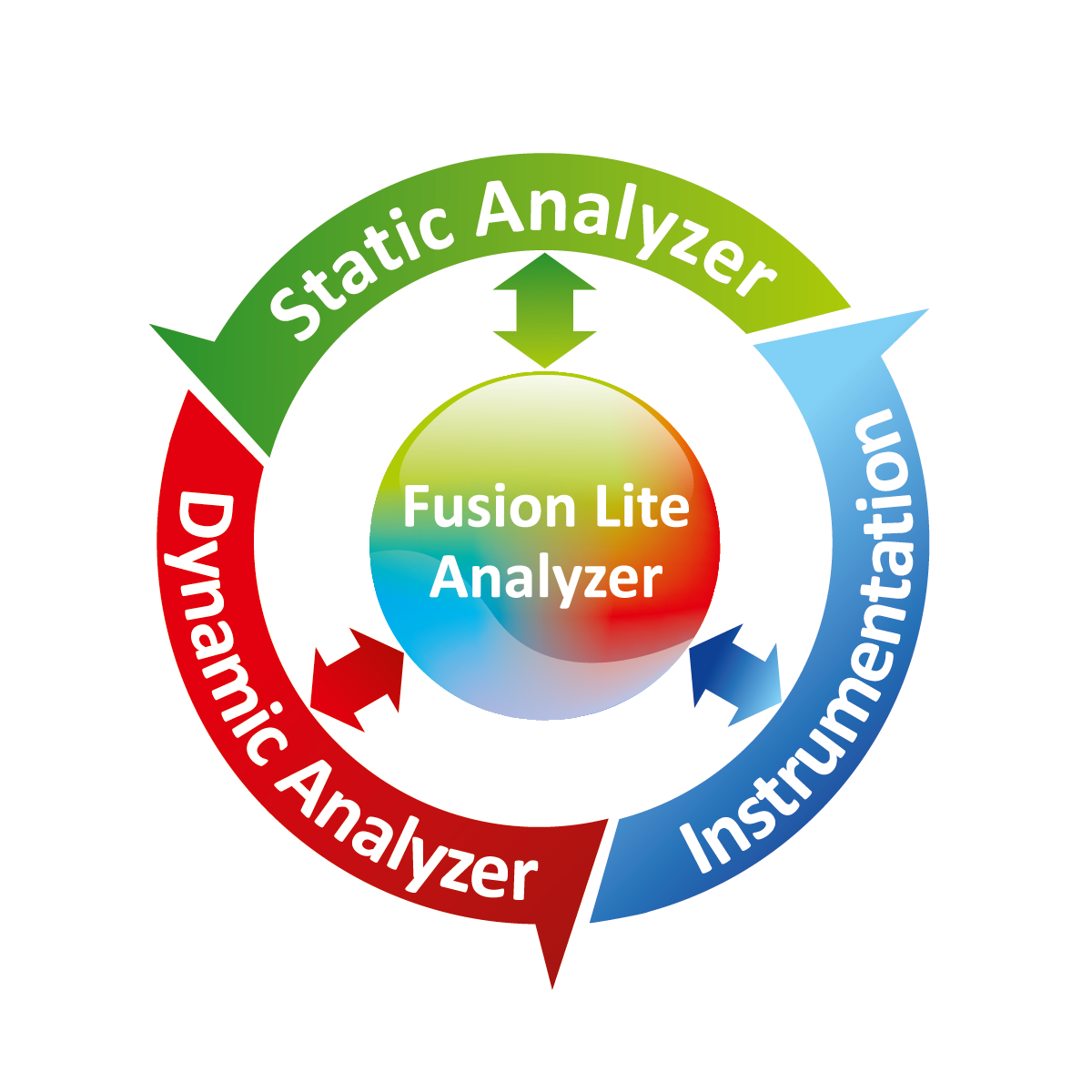
360° Integrated Analysis Technology
Fusion gives a 360° view of application in an integrated analysis environment which makes it seamless to analyze application from multiple perspectives (dynamic, runtime and code analysis) with power of multi-way coordination technology.
Amazing Insight with Deep Instrumentation
Fusion, with its deep instrumentation technology, gives an amazing insight into the internals of an application which enables smarter and deeper analysis resulting in significantly higher assurance compared to traditional approaches for application assessments.
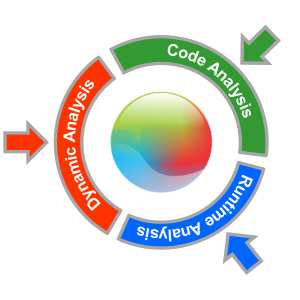
Fusion - 360° Integrated Analysis
Still paying for costly and separate IAST, SAST and DAST solutions? Get unmatched value with 3x Analysis at 1x Cost
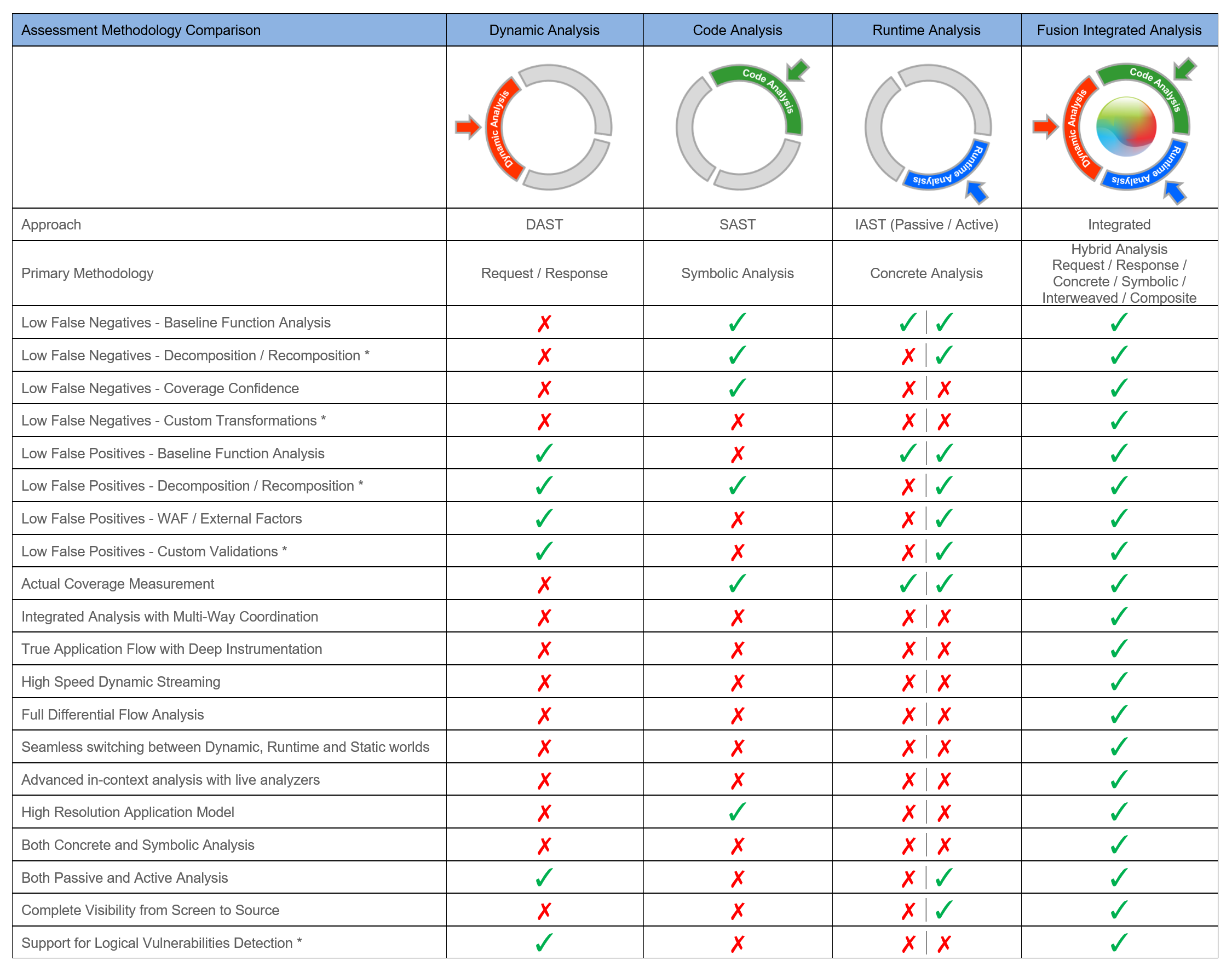
Running three types of analysis (DAST, SAST and IAST) separately on your application is not only costly but is also inefficient as they neither talk to each other nor provide live in-context analysis capabilities to security experts for advanced analysis.
Next-Generation Integrated Assessment
iAppSecure provides next-generation integrated assessment services that combine the power of dynamic, runtime and code analysis along with human intelligence. This gives customers an unmatched value with 3x benefits at just the cost of traditional dynamic assessment services.
Balancing Automation with Security Expertise
Automated DAST, SAST and IAST solutions primarily focus only on technical vulnerabilities. They completely miss critical business logic and authorization issues which often account for more than 50% of high risk findings. With integrated analysis service, customers get the best of both advanced technology and security expertise empowered with live in-context analysis capabilities.


Increased Assurance with 360° Integrated Analysis
FUSION TECHNOLOGY BASED ANALYSIS
Don't rely only on Dynamic and Static analysis for application security. Complement them with Runtime analysis for higher assurance.
Fusion Technology
Fusion is an innovative next generation technology from iAppSecure which radically changes the way applications are assessed.
Based on a subset of technologies from Fusion is Fusion Lite, which gives an amazing insight into the internals of an application enabling smarter and deeper application analysis.
APPLICATION ASSESSMENT SERVICES
Fusion Technology Based Analysis
iAppSecure's Fusion Technology based analysis leverages the power of Fusion, an innovative next-generation technology for application security analysis.

Integrated Analysis
Fusion includes dynamic, runtime and code analysis capabilities in a single integrated platform along with advanced multi-way coordination technology.

Amazing Insight
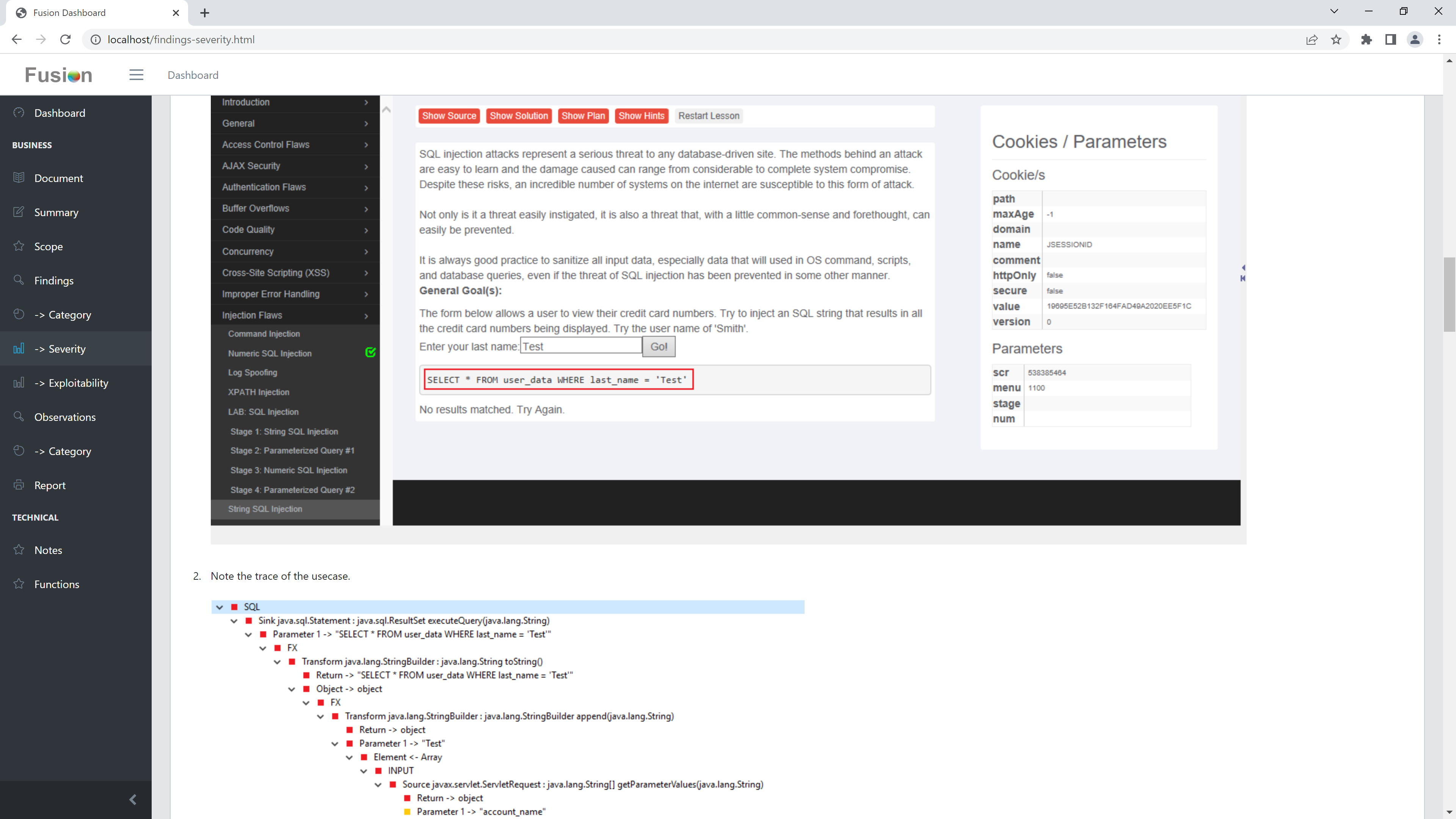
Fusion, with its deep instrumentation technology, gives amazing insight into internals of application which enables smarter and deeper analysis.

Higher Assurance
Fusion gives 360° view of application and ability to look at both positive and negative aspects of application which help provide higher assurance.

End-to-end Digital Recording
Fusion can capture application functionalities in great detail from user interface, to communication, to internal execution flow, to runtime code as evidence.

Technical and Logical Checks
We perform both technical and logical checks to achieve a broad coverage across various types of vulnerabilities and weaknesses.
Clear Actionable Reports
We provide clear actionable reports with prioritized findings and excellent end-to-end view from user interface to root cause of issue in application.

Protection of IP
Our technology can be deployed on-premise so that your code and data are analyzed within your organization for protection of your IP.

Cost Effective
Our model provides customers an unparalleled solution which not only leverages premium next-generation technology but is also cost-effective.
Assessment Methodology Comparison
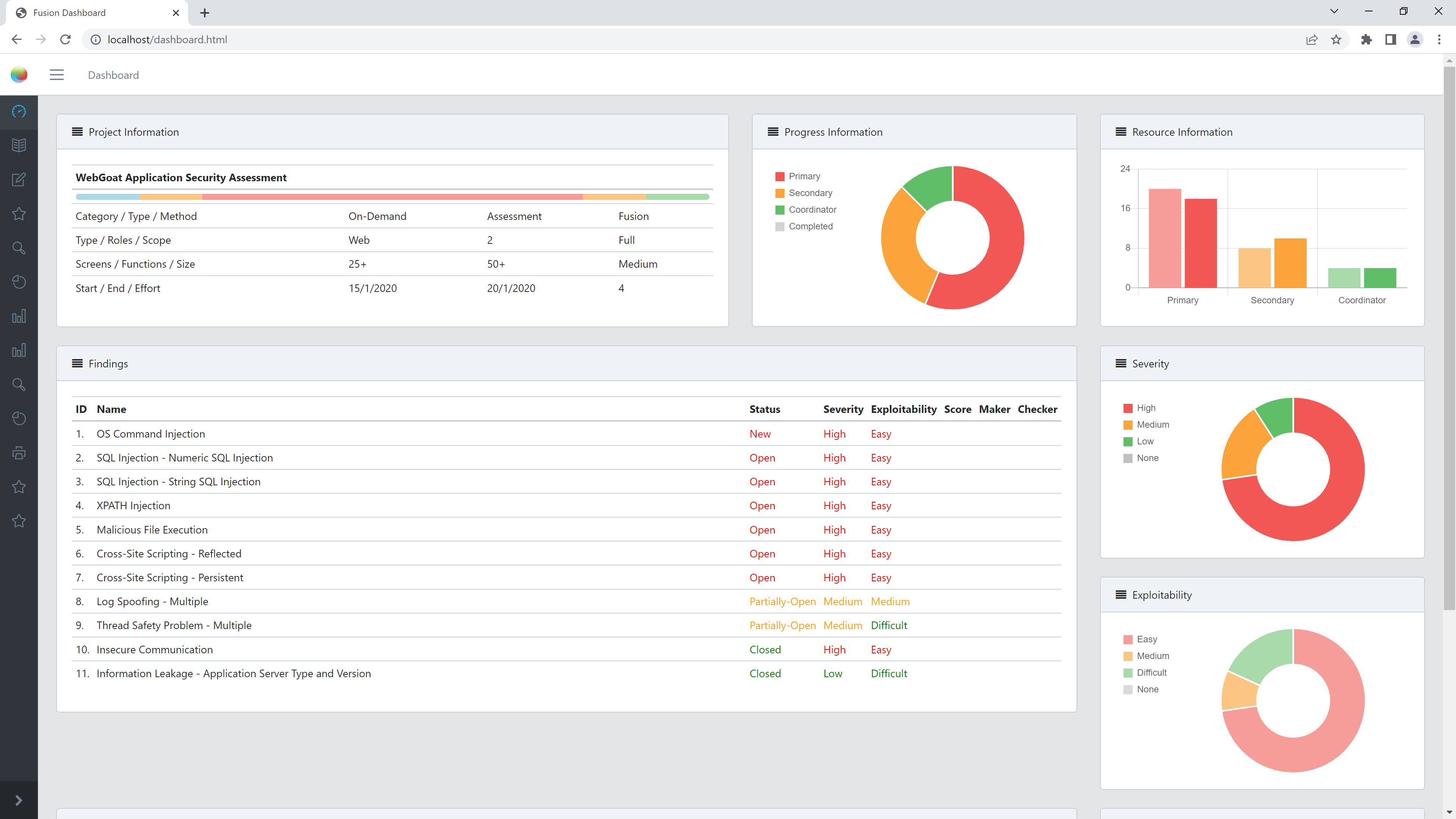
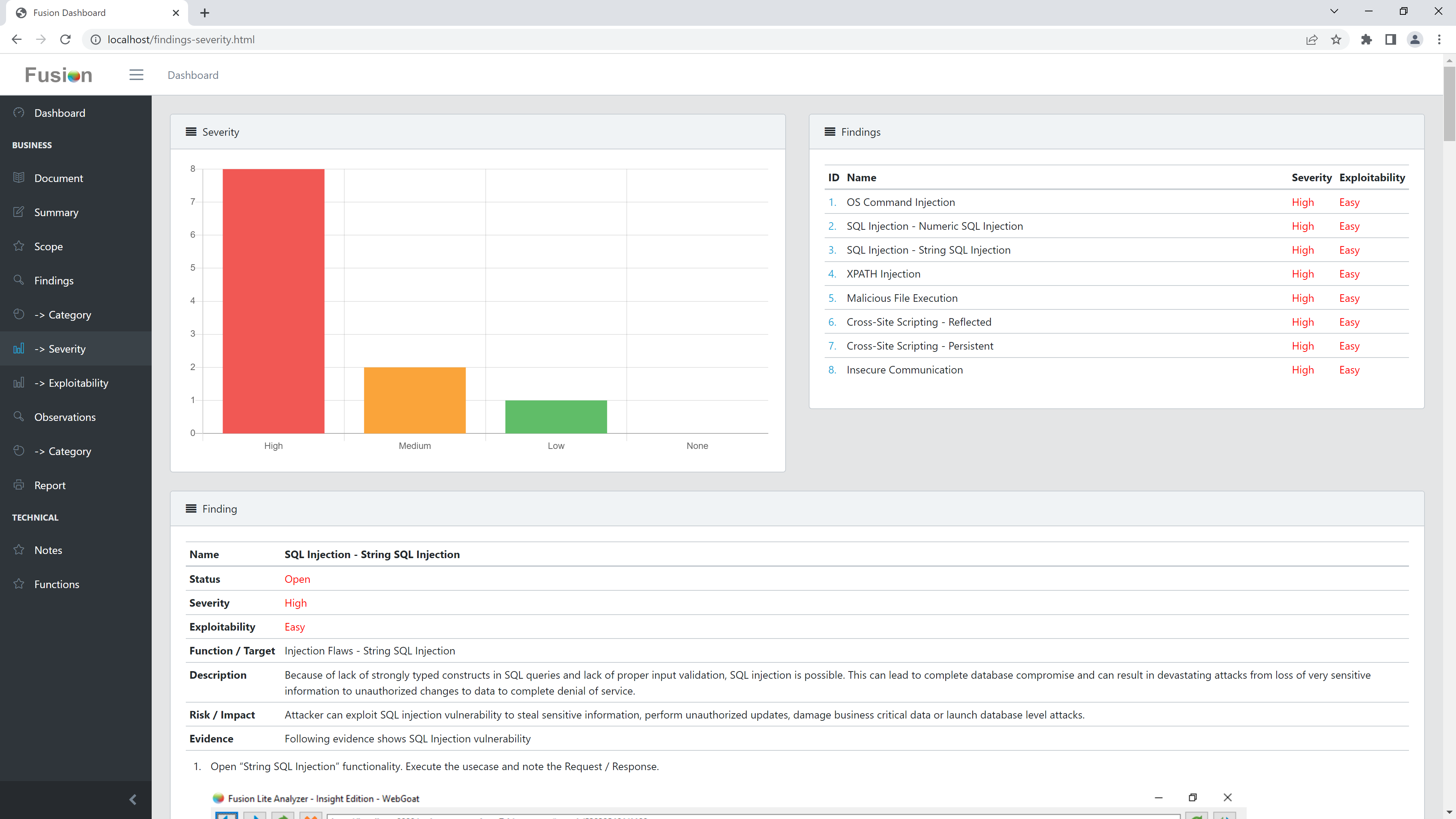
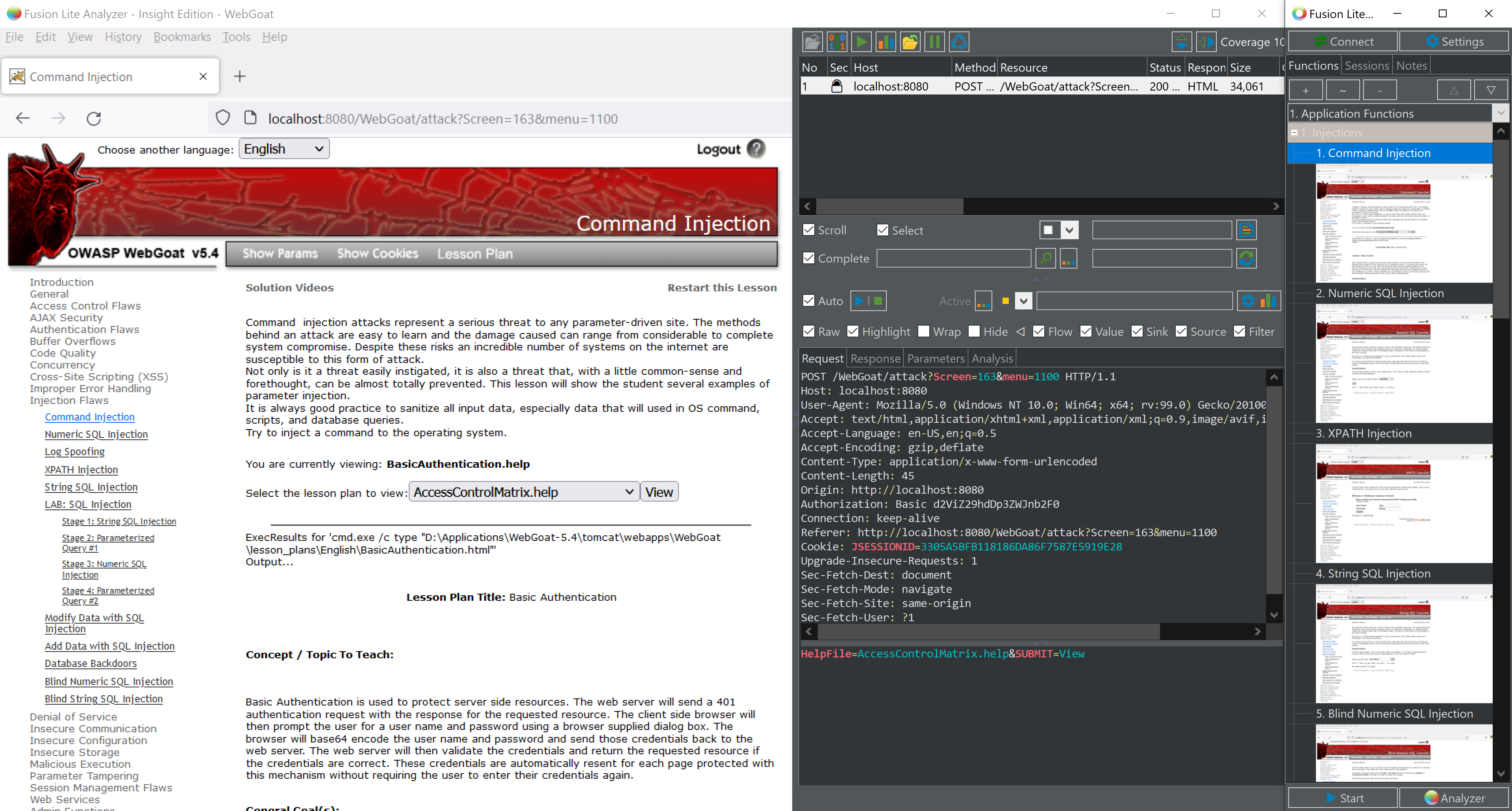
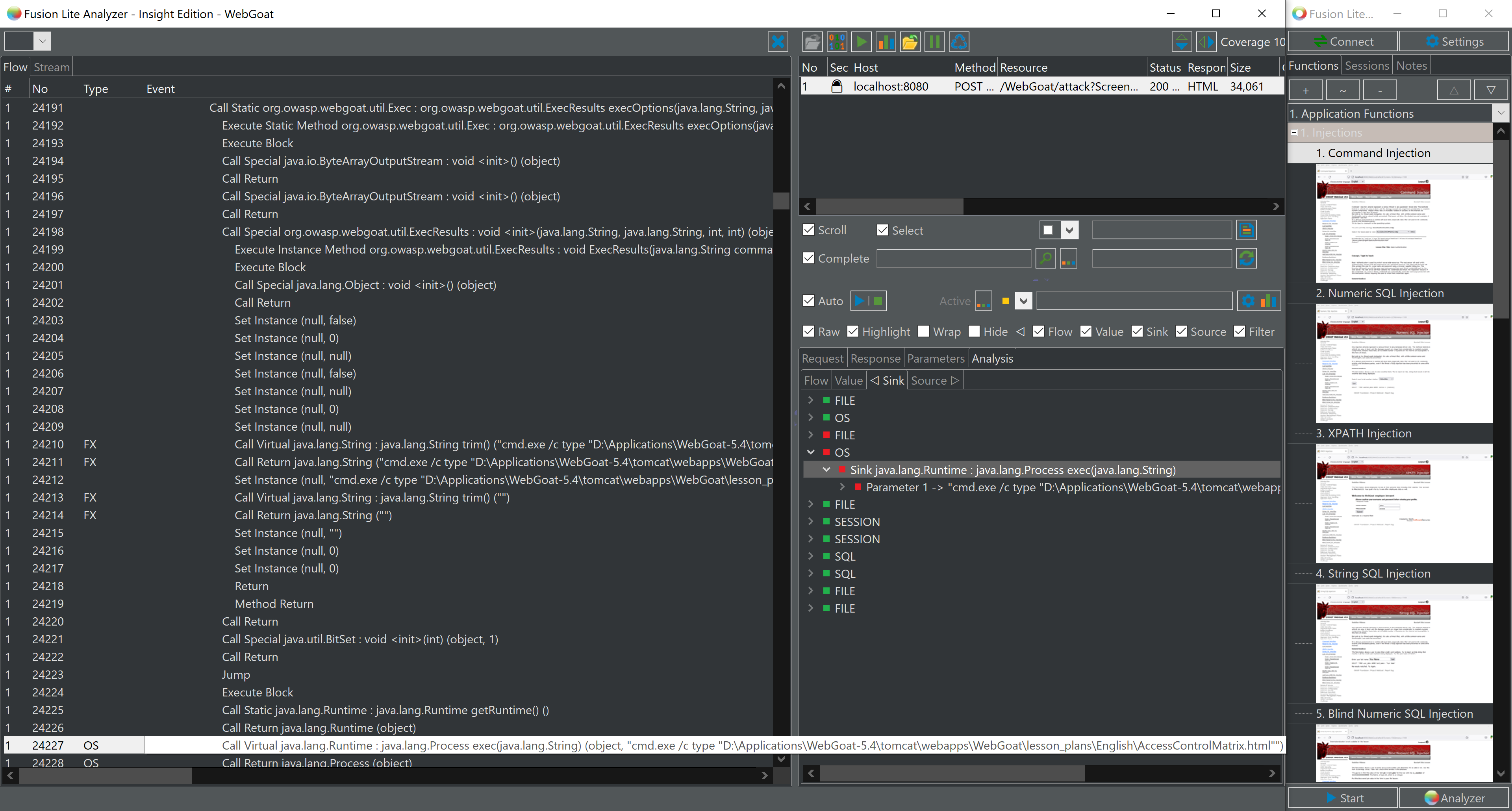
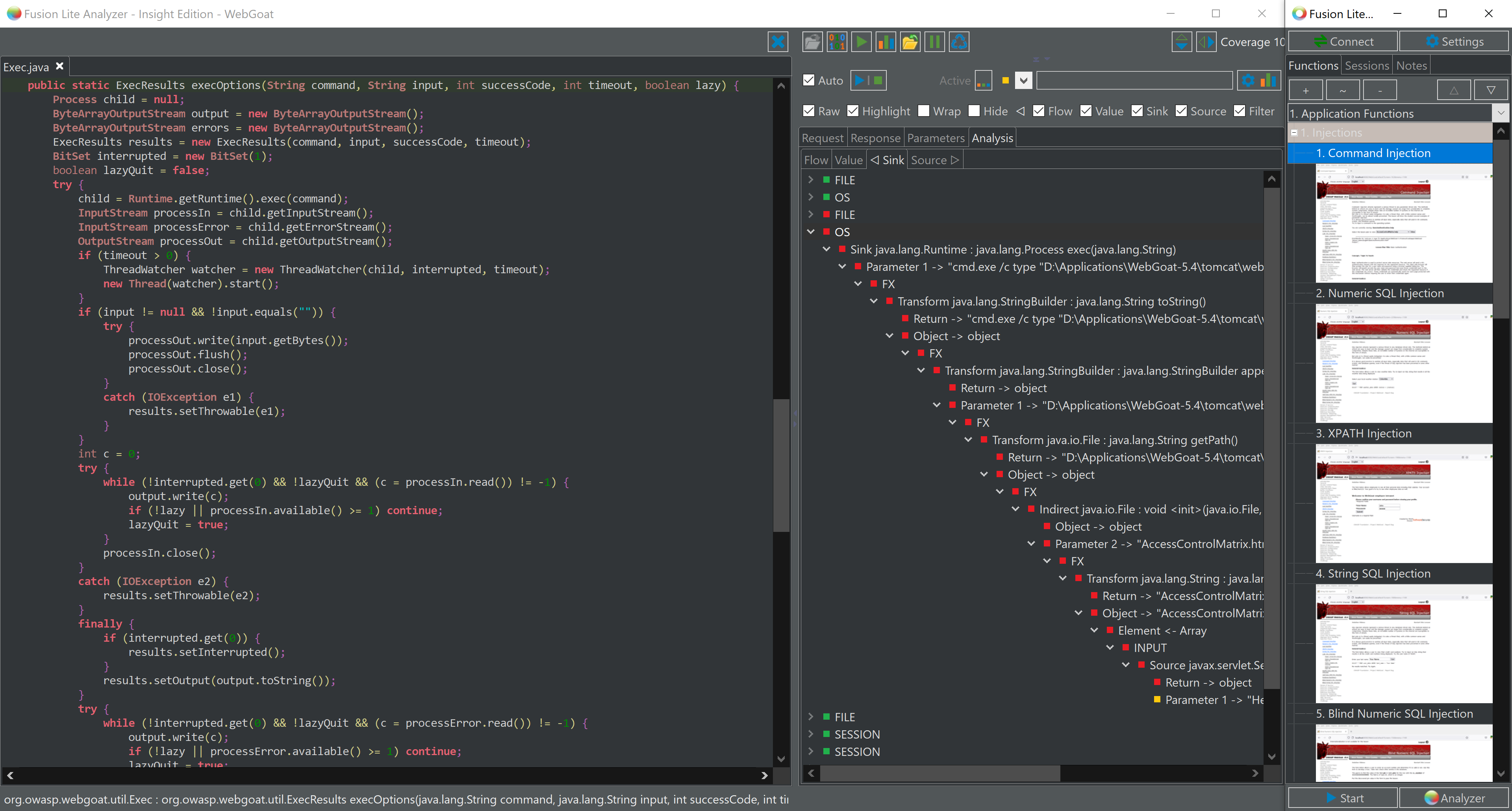
Fusion Dashboard
Fusion Dashboard gives a summary as well as a detailed view of findings which includes user interface, request / response, internal analysis trace, internal execution flow and mapping to source code as applicable which makes it very easy to understand complete anatomy of vulnerability or weakness.